How to set up a staging environment properly turns a risky deployment gap into a checkpoint where integration failures, performance regressions, and broken third-party connections surface before anyone notices. When staging closely mirrors production, teams gain a space to validate changes without risk, while browser-based sandboxes connected to the codebase let product and engineering review ideas before they ever reach that stage. This guide breaks down how to build staging the right way, without adding unnecessary overhead.
TLDR:
- A staging environment mirrors production to catch bugs, security issues, and integration failures before they reach real users.
- Production parity requires closely matching OS versions, server configs, and integration endpoints: scale down resources, not architecture.
- Environment drift costs teams $78K-$195K annually in lost productivity; prevent it by treating configs as code and rebuilding staging regularly.
- Strong staging workflows depend on automated testing, controlled access, and consistent deployment pipelines.
- Some browser-based sandboxes connected to real codebases let teams validate ideas early, so staging is reserved for final verification.
What Is a Staging Environment?
A staging environment is a replica of your production system where code gets tested before it reaches real users. Your staging environment should mirror live infrastructure as closely as possible, including server configurations, databases, third-party integrations, and environment variables. When staging diverges considerably from production, you reduce the reliability of the safety net it was built to provide.
Teams use staging as the final checkpoint before deployment. Bugs, broken integrations, performance regressions, and failed API calls all get caught here instead of in front of paying customers. Without staging or an equivalent validation layer, deployments carry considerably higher risk.
Why Staging Environments Matter for Product Teams
Shipping code without a staging environment is less of a workflow choice and more of a risk tolerance problem. The numbers make this clear: IBM research shows the average data breach now costs organizations $4.88 million, and 96% of organizations struggle with secrets sprawl across their environments. A misconfigured secret or exposed API key that slips past review into production can be catastrophic.
The cost of finding an issue in staging is a GitHub comment. The cost of finding it in production is an incident ticket, a rollback, and a customer apology.
Staging vs. Other Development Environments
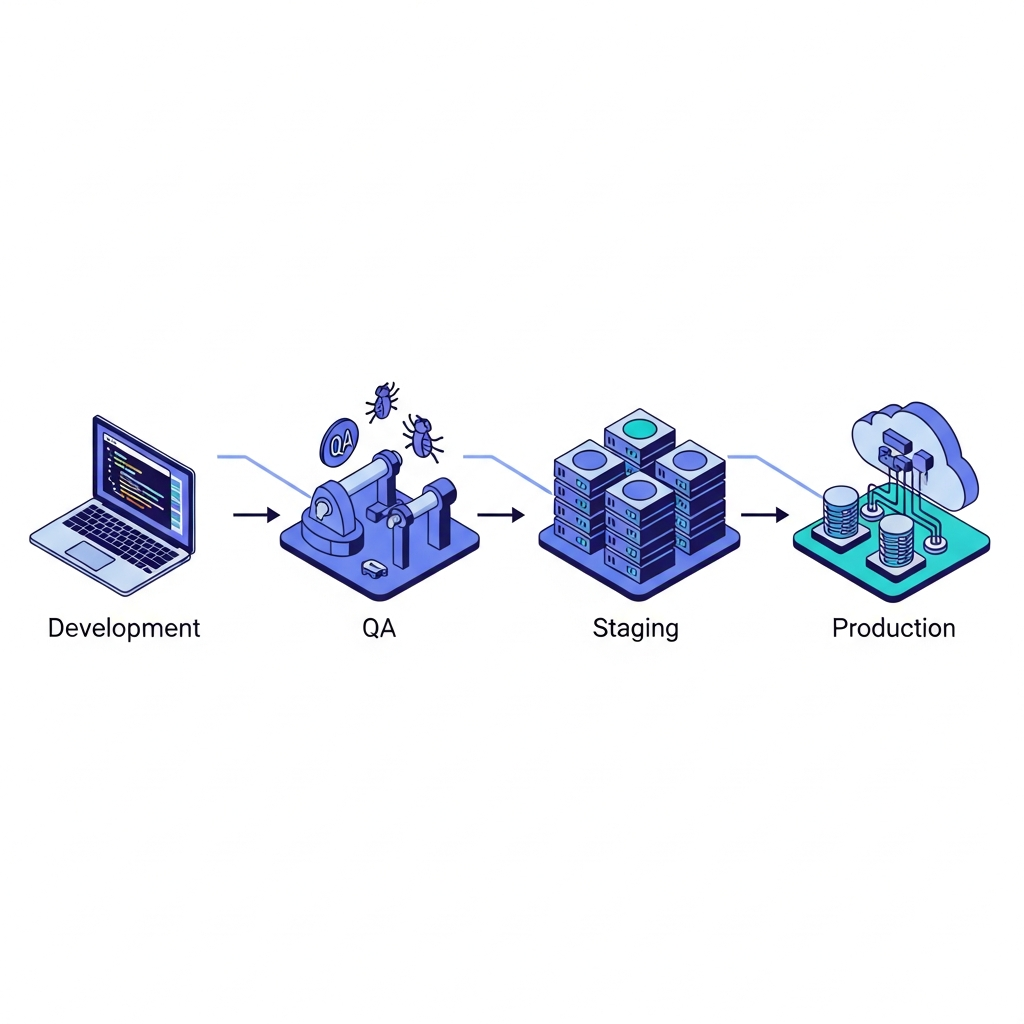
Many teams run multiple environments, each with a different role in the delivery process.
| Environment | Purpose | Audience |
|---|---|---|
| Development | Active coding and local testing | Individual engineers |
| QA | Functional and regression testing | QA team |
| Staging | Pre-production validation at full fidelity | Engineers, PMs, stakeholders |
| Production | Live system serving real users | Customers |
Staging sits directly before production for a reason. Unlike a dev environment, it runs on production-like infrastructure. Unlike QA, it goes beyond catching bugs to cover final integration checks, performance tests, and stakeholder reviews. The key distinction: staging tests the whole system together, not individual pieces in isolation.
Planning Your Staging Environment Setup
Start by auditing your production system and documenting every service, dependency, and integration your app touches. This becomes your staging checklist.
Key Decisions to Make Upfront
- What infrastructure will staging run on? The same cloud provider and region as production is ideal.
- Will you use full-size resources or scaled-down versions?
- Which third-party services need real sandbox accounts vs. mocked endpoints?
- Who needs access, and at what permission level?
- How will you handle production data without exposing real user information?
Resource Allocation
Most teams match production on architecture and configuration, but scale down compute and storage where load testing is not the goal. The exception is performance testing, where under-provisioned staging will give you misleading results.
Data Strategy
You need realistic data volumes and structures to catch real bugs, but you cannot copy live user data into a less-secured environment. Options include anonymized production snapshots, synthetic data generation that mirrors production schemas, and seeded test datasets maintained alongside your codebase. Pick one approach and standardize it.
Achieving Production Parity
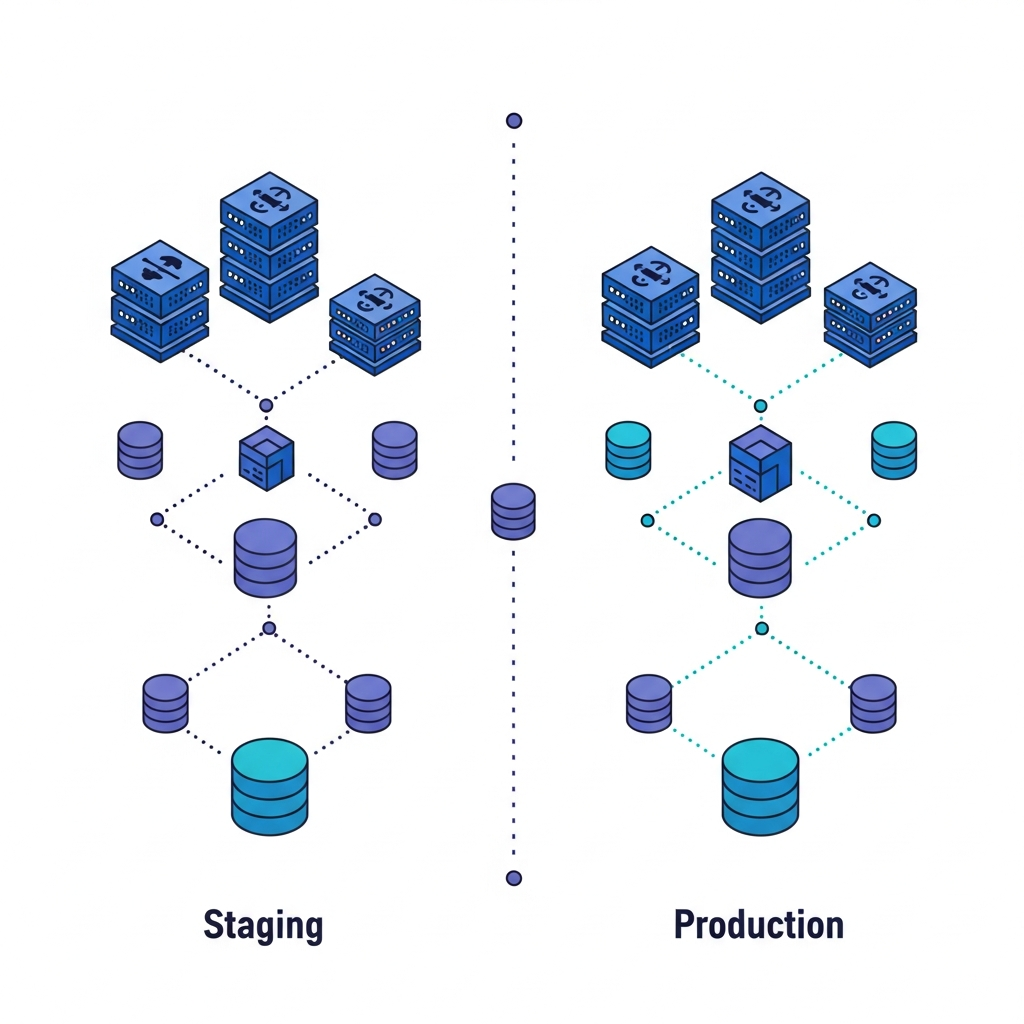
Production parity means your staging environment fails the same way production would under the same conditions. If a bug won't reproduce in staging, something almost certainly doesn't match.
What Requires Exact Matching
There are a few areas where you should avoid cutting corners:
- Operating system and runtime versions
- Web server and reverse proxy configuration
- Environment variables and feature flag states
- Network topology, including internal service routing
- Third-party integration endpoints (use sandbox accounts for critical paths; non-critical integrations may be mocked where appropriate)
Where You Can Reduce Costs
Smaller instance sizes are fine if you're not load testing. Replica counts for databases and cache layers can be reduced, and storage volumes can be trimmed as long as data structure stays identical.
The rule of thumb: match configuration exactly, scale resources proportionally.
Configuration drift is the quiet killer. Use a secrets manager like AWS Secrets Manager or HashiCorp Vault to keep environment variables consistent across environments. Never hardcode values that differ between staging and production. Treat your staging config as code, version it, and review changes the same way you would a pull request.
Setting Up Your Staging Infrastructure
Infrastructure as Code
Define your staging environment in code using Terraform, Pulumi, or CloudFormation. This keeps staging reproducible, reviewable, and easy to rebuild when it drifts. Store these configs in version control alongside your application code.
CI/CD Pipeline Setup
Your pipeline should deploy to staging automatically on every merge to your main branch. The basic flow:
- Build and run unit tests first to catch regressions before anything gets deployed
- Deploy the build artifact to your staging environment
- Run integration and smoke tests against the live staging instance
- Gate production deployment on passing results so broken code never ships
Database Configuration
Provision your database using the same engine version and schema as production. Populate it using whichever data strategy you chose during planning, whether anonymized snapshots or synthetic seeds, and automate that seeding step so every staging refresh starts from a known state.
Managing Environment Drift
Environment drift happens quietly. A config value gets updated in production during an incident fix. A feature flag gets toggled and nobody updates staging to match. Over time, staging stops reflecting reality, and its value erodes without anyone noticing until a bug slips through.
The cost compounds fast. A ten-engineer team losing two hours per sprint to staging contention and coordination burns through $78,000 annually at a $150/hour fully loaded rate. At 25 engineers, that figure crosses $195,000.
Prevention comes down to three habits:
- Treat all configuration as code and run it through version control and peer review, so changes are visible and reversible.
- Automate regular drift detection by comparing staging and production configs on a schedule, instead of waiting until someone suspects a problem.
- Rebuild staging from scratch periodically using your Infrastructure as Code definitions, so accumulated manual changes get wiped before they calcify.
Security and Access Control Best Practices
Staging often connects to real third-party services, holds anonymized but structurally real data, and runs on infrastructure that shares network boundaries with production. Here are the access controls worth putting in place:
- Require SSO authentication instead of shared credentials, so access is tied to identity and can be revoked instantly when someone leaves a team.
- Apply role-based permissions so developers, QA, and stakeholders get only what they need.
- Restrict public access by default and allowlist IPs where possible.
- Rotate secrets on a schedule and store them in a dedicated secrets manager, never in
.envfiles committed to version control.
Testing and Validation Workflows
Four test categories matter most in staging:
- End-to-end tests covering critical user flows like checkout, authentication, and onboarding to confirm the full experience works as expected.
- Integration tests that validate third-party service connections under realistic conditions, using real services for critical paths and mocks where appropriate.
- Smoke tests confirming core functionality after every deployment, so regressions surface immediately.
- Performance tests before major releases, run against production-equivalent load to catch bottlenecks early.
Share a staging link, collect feedback asynchronously, and gate production deploys on sign-off. Automate what you can, document what you cannot, and run the same sequence every time.
Common Staging Environment Pitfalls
Most staging failures trace back to the same short list of mistakes.
- Skipping data realism: synthetic data that doesn't mirror production schemas lets bugs hide until they hit real users.
- Deploying differently to staging than production: if staging uses a manual script and production uses a CI/CD pipeline, you're not testing the same thing.
- Treating staging as permanent: environments accumulate manual changes over time and quietly stop reflecting reality.
- Restricting access too broadly or too loosely: stakeholders locked out can't give feedback; too-open access creates security gaps.
- Skipping the environment entirely under deadline pressure: this is when it matters most, not least.
Write the rules down, automate the enforcement, and stop treating staging as optional.
Moving from Staging to Cloud Playgrounds with Alloy
Staging works best when ideas arriving at that checkpoint have already been pressure-tested. Features often reach staging half-formed because there was no earlier layer to validate them.
Alloy fills that gap. As a Cloud Playground, it connects directly to your real codebase and spins up isolated, shareable sandboxes in seconds, no infrastructure config required. Product managers and designers can experiment with UI changes, test new flows, and collect stakeholder feedback through a browser before a single engineering hour gets committed to a formal staging deployment. With recent performance improvements delivering 2x faster build and design operations, the window from idea to interactive prototype is now minutes, not days.
The workflow plugs into tools you already use. Jira and Linear integrations keep experimentation tied to your roadmap, so ideas move from Cloud Playground to staging to production without falling out of context. Folder-based organization lets teams manage parallel experiments across multiple feature areas, and contextual commenting means feedback happens directly on the prototype instead of in a separate thread.
The practical effect: fewer half-baked features reach staging. When teams validate earlier, staging gets used for what it was always meant to do: final production-readiness checks, without doubling as an exploration space. That makes every step of the process sharper.
FAQs
How long does it take to set up a staging environment?
The initial setup can take anywhere from several hours for a simple application to several days for more complex systems, depending on infrastructure and integrations.
Can I use real production data in staging?
No. You should generally avoid copying live user data into staging due to security and privacy risks unless it is properly anonymized and compliant with regulations. Instead, use anonymized production snapshots, synthetic data that mirrors production schemas, or seeded test datasets maintained in version control.
Why would I need both a staging environment and Alloy?
Staging validates production-ready code before deployment, while Alloy helps you test and validate ideas before they ever reach staging. Alloy's Cloud Playground lets product teams experiment with features and gather feedback in minutes, so only well-vetted concepts consume formal staging resources.
Final Thoughts on Your Staging Workflow
Knowing how to set up a staging environment well comes down to one thing: making it a true reflection of production so nothing slips through unnoticed. When staging is reliable, deployments stop feeling risky and start feeling routine. Alloy strengthens that workflow by helping teams validate ideas before they ever reach staging, so what arrives there is already well-formed and ready for final checks. With that upstream clarity in place, staging becomes a sharper checkpoint instead of a bottleneck.

